Remove LEAKS Ransomware

The LEAKS Ransomware is a threat that you must keep away from your computer all costs. This is because recovering from its attack can be a very complex challenge. Unlike traditional malware, you cannot recover from LEAKS Ransomware's attack by simply eliminating the threat. The goal of this ransomware is to encrypt the files on your device and then extort you for money. Unfortunately, removing the malware will not undo the damage it caused – you will still be unable to access your data.
The LEAKS Ransomware appears to be an advanced malware family, which also steals files prior to encrypting them. This is a growing trend among ransomware creators – it gives them another chance to extort the victim for money. Not only do they sell a decryption tool, but they also threaten to leak the data they stole online. Needless to say, the latter is a situation that victims certainly want to avoid.
LEAKS Ransomware Steals Files and Threatens to Publish them Online
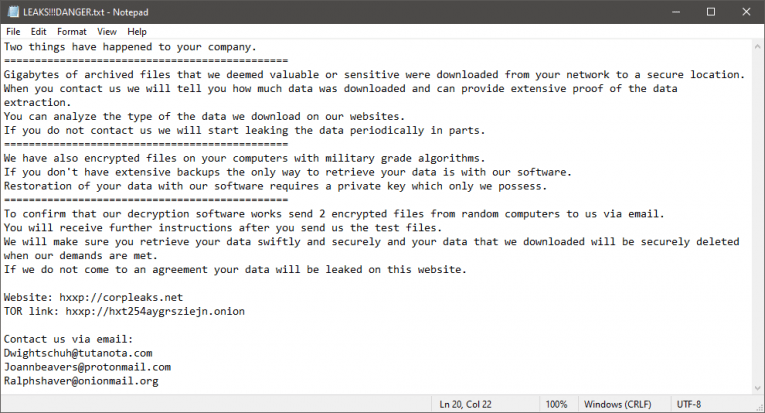
Ransomware that also features data theft functionality is often employed in attacks against businesses and organizations. This is because they are more likely to agree to pay a ransom fee in order to keep their data private. The files that the LEAKS Ransomware locks will be recognizable by a change to their name – they will have the '.LEAKS' extension next to their original name. Another system change that the LEAKS Ransomware brings is to wipe out Shadow Volume Copies and to drop the 'LEAKS!!!DANGER.txt' document. This file lists the contact details of the criminals:
- The public website corpleaks.net – also used by other ransomware families.
- The emails Dwightschuh@tutanota.com, Joannbeavers@protonmail.com, and Ralphshaver@onionmail.org.
- A TOR-based payment portal.
Victim of the LEAKS Ransomware? You should not accept the offer of the criminals. Even if you pay up, they may opt to scam you or try to extort more money out of you. The best way to proceed is to eliminate the malicious software with the help of an antivirus tool. After this, experiment with popular data recovery software.








