Remove Bengalcat Ransomware

Ransomware attacks continue to be the number one threat online. These dangerous threats are being spread through the use of email attachments, pirated downloads, and other deceptive content. The best way to stay protected from them is to use reputable antivirus software. In addition to this, we recommend relying on backup services to maintain reserve copies of your files. A relatively new file-locker being spread online is called the Bengalcat Ransomware. It has the ability to encrypt files, and then offer to sell a decryption tool to the victim.
While Bengalcat Ransomware's attack sounds very dangerous, there is some good news. The Bengalcat Ransomware's creators have used the HiddenTear project as a foundation for their malicious program. This means that the Bengalcat Ransomware uses a flawed file-locking mechanism, which may allow users to restore their data through a free decryptor. In order to do this, victims need to use the free HiddenTear decryptor to try and accomplish the task.
'.777' Extension Marks Files that the Bengalcat Ransomware Locks
But how does the Bengalcat Ransomware attack look like? After the ransomware executes its attack, it will add the '.777' extension to the files it locks. In addition to this, it drops the 'read_it.txt' ransom message for the victim to read. The good news is that the Bengalcat Ransomware does not delete System Restore Points or Shadow Volume Copies. The criminals' message says that they have stolen important files and databases, but this is a bluff – the Bengalcat Ransomware does not have such abilities.
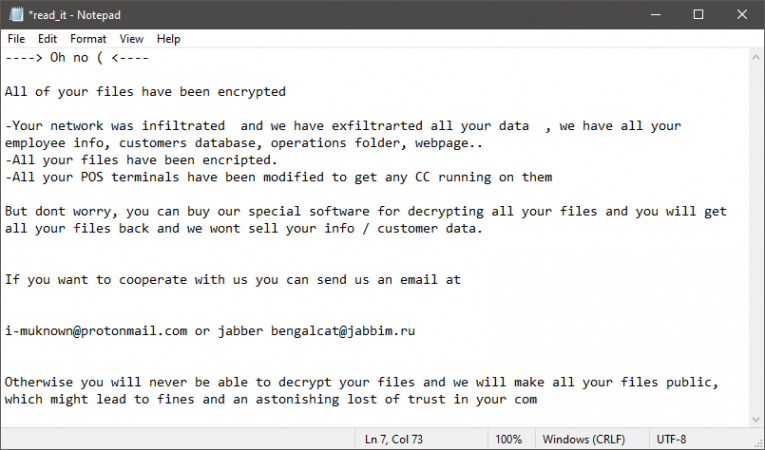
Before running the free decryptor, victims of the Bengalcat Ransomware need to eliminate the malware with the help of an up-to-date antivirus scanner. The criminals do not mention the price of their decryptor, but you can be sure it is not cheap. It is never a good idea to co-operate with ransomware creators, because there is always a risk of being scammed. The Bengalcat Ransomware operators mention the email i-muknown@protonmail.com and the Jabber ID bengalcat@jabbim.ru for contact. You should not get in touch with them – instead, follow our advice above to eliminate the threat, and recover your files.








