Remove Army Ransomware
Dealing with the consequences of a file-locker attack can be very challenging, especially if you are dealing with one of the high-profile malware families. Thankfully, some ransomware creators still lack the skills and knowledge to create high-level malware. This is the case of the developers of the Army Ransomware. This threat is part of the Xorist Ransomware family and, thankfully, many of these file-lockers are decryptable via free tools.
Victims of the Army Ransomware will have their data locked, and the names of the damaged files will be changed to include the '.army' extension. Another change that the Army Ransomware makes is to drop the ransom message 'HOW TO DECRYPT FILES.txt.' The ransomware will also attempt to wipe out System Restore Points and Shadow Volume Copies, therefore hindering the effectiveness of 3rd-party security tools.
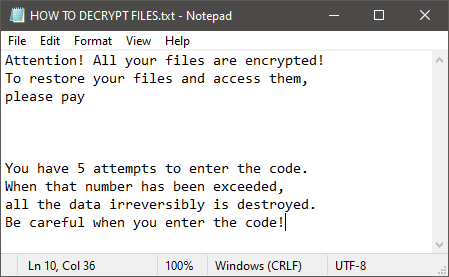
The ransomware also spawns a window asking the victim to enter a password to unlock their keys. The message says that the victim has five attempts to enter the correct code – otherwise, their data will be destroyed. Allegedly, Army Ransomware's victims can purchase the password for Bitcoin, but the criminals have not provided contact or payment details. Thankfully, it might be possible to undo the damage that the Army Ransomware does. This can be done with the use of one of the free 'Xorist Decryptors' available online. Keep in mind that you will still need to use an up-to-date antivirus tool to terminate the ransomware fully and prevent it from causing more damage. Other Xorist variants that may be decryptable are the XiNo Ransomware and the Lohodf Ransomware.
Do not forget that it is best to take the necessary measures to prevent threats like Army Ransomware from attacking you in the first place. Avoid browsing suspicious sites, never download unknown files, and keep your system protected by antivirus software at all times.








