Want to Survive Ransomware - Here's How to Protect Your PC
IT security experts have argued that “ransomware is everything bad about humanity distilled into malware—maliciousness, greed, and casual incompetence”. It’s not difficult to see why some of them could hold that opinion – it is one of the most pernicious and profitable forms of attack, and is unfortunately very successful and widespread, which is why users need to know how to protect themselves from it.
Table of Contents
What is Ransomware?
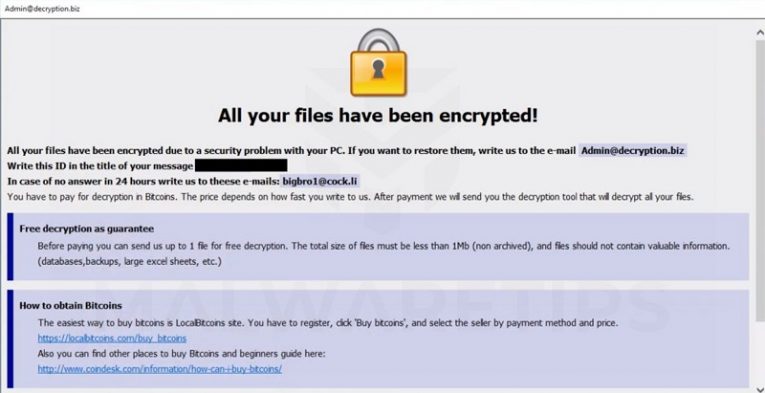
Ransomware is a pernicious sort of malware that is designed to lock the user out of the use of the affected device until a “ransom” is paid. This is usually done by the malware encrypting all the files on the device, rendering them unusable without a decryption tool or key. The ransom demanded is usually in some form of cryptocurrency. While ransomware is most effective as a tool for extorting corporate, enterprise, and government entities, private individuals are also often affected by such malicious attacks.
How to Protect Yourself From Ransomware
- Users need to be thoroughly educated on what ransomware is, what the most common vectors of infection are, and what the consequences of malicious actors getting a foothold on your system may mean for it. Malicious actors in the IT-sphere are ingenious and are only getting more active, not less – which means that users need to keep up with them constantly. While that may appear like a sub-optimal use of your time, it may well prove invaluable for avoiding a data-disaster.
- Users need to prioritize figuring out what IT security solutions are best suited for them and their particular situation, then proceed to implement said solution post haste. The scope and nature of the measures taken to ensure optimal IT security guaranteed by specialist activity may vary – for most users, just running an adequate anti-malware app on the few devices that they use can be sufficient.
- It is imperative that any user that values their data adopts a method of storing their files reliably. That way if said data is lost to a malicious ransomware attack, it could be recovered with relative ease.
What Means of Data Storage you Could use?
- Local data storage. Some companies prefer to keep a dedicated device loaded with backups of all the data relevant to their activities. While this method is certainly not bad and may ensure that no data is lost in a cyber-attack, it still carries the risk associated with storing your information in one physical device – it needs to be maintained, and technical breakdown in said device at a bad time can invalidate all the effort the entire company’s put into data backup to date.
- Cloud data storage. There are services that specialize in providing both general data storage services, and dedicated data storage spaces for companies optimized to fit the particular needs of their clients. This is an excellent option, as it both makes any data you wish to store readily accessible for recovery at any time in any place and extremely well protected.
How to Remedy a Ransomware Infection
Finally, if a user ever has the ill-luck of falling victim to a ransomware attack, they should not despair - all hope is not lost. There are free tools and steps you can take to counter the encryption used by some types of ransomware. Here are a few examples:
- No More Ransom is a rather spectacular joint project between McAfee and a handful of European law enforcement organizations that now boasts about 100 corporate and government partners. If a user’s system is ever infected, said user could try to upload some files to the No More Ransom site. If any of the experts involved in the project has a solution for this type of encryption, the victim will be given the opportunity to unlock their files at no cost.
- ID Ransomware is a project similar to No More Ransom but is a project created and run by Emsisoft.
- Ask around and get in touch with IT security specialists that focus on preventing and countering this type of attack. Twitter is a good place to try and get a hold of them, and most of them are super helpful when it comes to recovering files.








