Remove JamesBond Ransomware

The JamesBond Ransomware is a low-quality piece of malware. It is able to encrypt data on the computers it infects. Its creators use the locked files as an opportunity to extort the victim for money. They ask them to pay a ransom fee in exchange for a decryption tool. There is some good news though. The JamesBond Ransomware is based on the HiddenTear project, which is likely to mean that a free decryption option is available. You will not need to send money to the attackers. You can run the free decryptor to try and recover the decryption key. However, keep in mind that this method does not always work, despite its high success rate. Even if it does not work for you, you should not consider complying with the demands of JamesBond Ransomware's creators.
JamesBond Ransomware - a new HiddenTear Variant?
This threat usually infects victims through dangerous files they download from fraudulent emails, torrent trackers, or sites hosting pirated content. Once this ransomware runs, it will immediately get to work. Its goal is encrypting valuable files like media, documents, archives, etc. It will also mark their names with the suffix '.jamesbond2021@tutanota.com_jamesbond.' The ransom note it uses is titled 'read_it.txt' – the same file that HiddenTear uses by default.
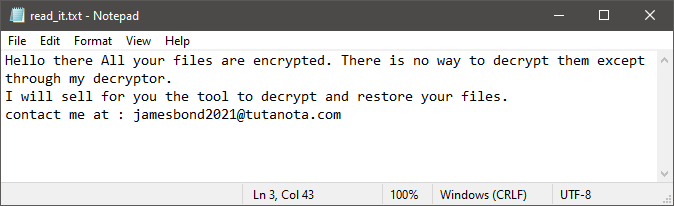
According to the ransom message, victims must ask the attacker for help by messaging them at jamesbond2021@tutanota.com. The crook claims that there is no other decryptor, and victims must co-operate if they want help. Needless to say, this is a bluff. Its goal is to convince you that paying a ransom fee is the only way to get your files back. Ignore the offer of the criminal, and look for alternative data recovery options. Of course, first make sure to eliminate the JamesBond Ransomware fully. The best way to take care of this with ease is to run a reputable anti-malware software suite.








