The Admin Locker Ransomware Attack - How to Recover From It?
Admin Locker Ransomware is a piece of malware, which could cause long-lasting damage to your most valuable files. Threats like this often lurk on shady websites associated with the distribution of pirated media, game cracks, or software activators. We advise you to stay away from such Web destinations at all times, and to always use up-to-date antivirus protection if you happen to visit such pages. Needless to say, you should not download anything from random, non-trustworthy sites – or you might come across threats like this one.
The Admin Locker Ransomware Attack
When this file-encryption Trojan is run on an unprotected system, it will immediately get to work in the background. The goal of the attack is to encrypt the majority of the victim's important files. This is why the Admin Locker Ransomware goes after documents, media, archives, databases, and other common file formats first. It will also intentionally skip encrypting file formats such as DLL or EXE – this ensures that the system will continue to be operational.
All files it locks are marked with a random variant of the '.admin' extension. It is not clear how the ransomware decides what extension to use, but some of the common ones are admin1, admin2, 2admin, 3admin, etc.
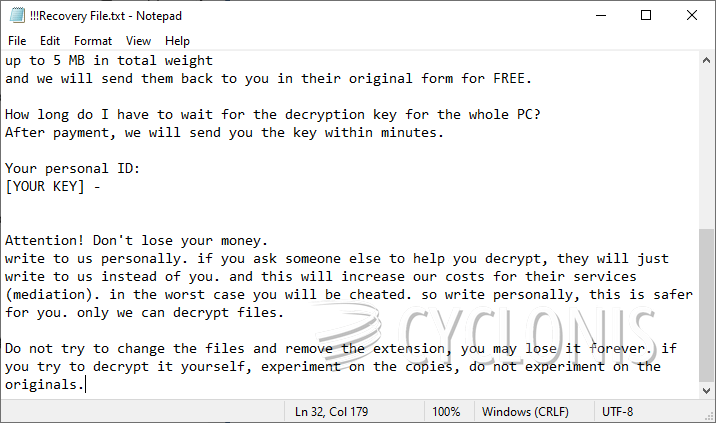
After the attack is complete, the Admin Locker Ransomware drops the '!!!Recovery File.txt' ransom message. It refers victims to a TOR-based support site, and also mentions a Telegram ID where the criminals can be messaged. We advise you not to try to get in touch with them, or to attempt to purchase a decryption tool – you will probably get scammed. The best option for victims of the Admin Locker Ransomware is to run an up-to-date security scanner, and then explore alternative data restoration utilities.








