Remove Loki Locker Ransomware

File-encryption Trojans continue to be a great cyber threat. They are spread by using all sorts of tricks, and their criminals are after your money. However, instead of outright stealing your money, they want to convince you to send it to them. They do this by encrypting your data and then offering to unlock it for money. The Loki Locker Ransomware's creators are using the exact same strategy. Unfortunately, victims who fall victim to this ransomware attack might not be able to get their data back easily. The Loki Locker Ransomware uses a flawless mechanism to lock files, and it cannot be decrypted via free tools.
If you run the Loki Locker Ransomware on an unprotected device, the threat will execute the attack immediately. It needs just a few minutes to encrypt the contents of important files, rename them, and then disable System Restore / Shadow Volume Copies. This further limits the victim's data recovery options.
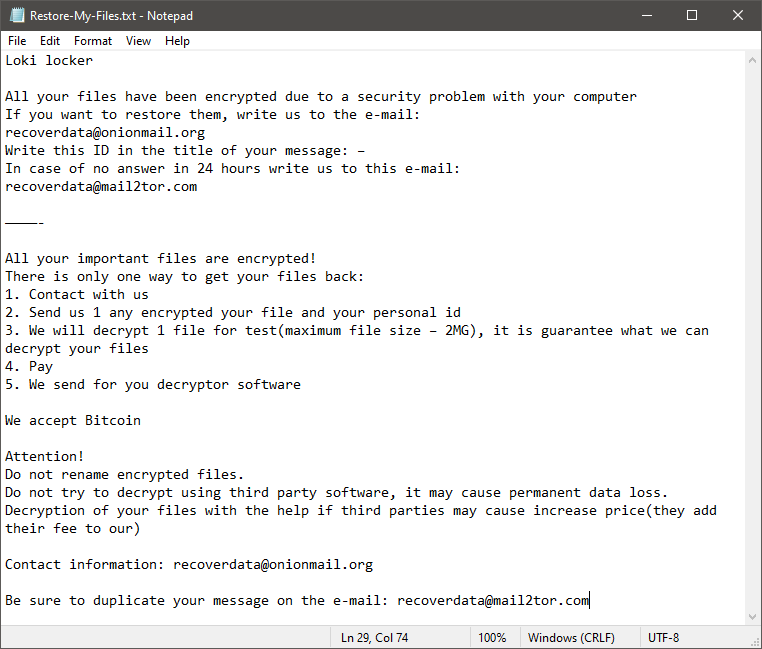
The files that the Loki Locker Ransomware locks are recognizable because of their modified name. This file-locker uses the following pattern – [recoverdata@onionmail.org][<VICTIM ID>]<ORIGINAL FILENAME>.Loki.' It also delivers the document 'Restore-My-Files.txt' – it contains a message from the attackers.
The criminals ask the victim to pay a ransom fee and contact the criminals via the emails recoverdata@onionmail.org and recovedata@mail2tor.com. However, trying to co-operate with them is not a good idea. They offer no proof that they are trustworthy. Even if you pay, they may scam you. Our suggestion is never to agree to the offers of ransomware creators. Instead, run an anti-malware application to eliminate the threat. After this, seek alternative data recovery options and software.








