The Challenges of Storing Passwords Correctly and Safely

The process of recovering access to an online account could be quite a hassle. Sometimes, you need to get in touch with a support agent who'll ask you all sorts of questions before finally giving you a link with which you can create and assign a new password for your account.
With some services (not too many), however, recovering a password is nice and easy. You click a Forgot Password button, and a computer or a person sends you an email with the password you've forgotten. You might be feeling happy with how convenient a system that works like that is. And convenient it is indeed. What you may not realize, however, is that the said system is handling your password in an extremely insecure manner.
First of all, email is not the most secure form of communication. There are exceptions, but most of the mainstream email providers don't encrypt the information in the messages, which means that it can be stolen in transit. That's not the only problem.
The fact that the password is sent to you in plain text means that it's likely stored in plain text too. And this means that if hackers get their hands on it, there will be nothing to stop them from taking over your account. Your password might also be stored in encrypted form, but that's not a good practice, either. If it's encrypted, it can be decrypted with keys that could get exposed. And you never know when a disgruntled employee will decide that you are the reason for their unhappiness.
So, service providers shouldn't store your passwords in plain text, and they shouldn't encrypt them. What, then, is the correct way of keeping them safe?
How do responsible service providers store your passwords?
The mathematical operation website owners should use is called hashing. A hash function converts your password into an unreadable string of characters (called a hash value or, simply, a hash) that has no visual resemblance to the actual password. For example, if you use the SHA1 hashing algorithm (it's an old algorithm that isn't terribly secure, but we're using it for illustrative purposes), the hash value of "password" is "5baa61e4c9b93f3f0682250b6cf8331b7ee68fd8". The hash is then stored in a database and is compared to a hash of the password you enter when you're logging in.
Encryption also turns your password into an illegible string of characters, but, provided the decryption keys are present, the encrypted password can easily be turned back into the plain text one. Hashing is supposed to be a one-way action, meaning that if the hashing algorithm is good enough, even automated tools running on powerful hardware will need quite a lot of time to crack the hash and retrieve the password. As a result, neither unhappy employees nor hackers will be able to see your password.
The problem is, the same password produces the same hash under the same algorithm, and because so many people use "123456" to protect their accounts, a password can be guessed based on the hash. That's why service providers should also salt your password. Salting effectively means that they're adding a string of characters (for example "QxLUF1bgIAdeQX") to the end of your password before hashing it. Every user should get their own, unique salt meaning that even if your password is the same as the password of, say, your neighbor, the hashes will be completely different. This doesn't mean that using common or simple passwords is fine, but proper hashing and salting does make the hackers' job more difficult.
Of course, there's a lot more to it than that, but what you just read has hopefully given you a basic understanding of what steps website owners and service providers should take when they're setting up their authentication systems. Sadly, the fact that online accounts get compromised day in, day out means that not all of them have been sticking to these basic security principles. And unfortunately, there's nothing you can do about it.
Once you give your password to a website, you put your trust in the people behind it to keep your data safe. You have no control over what happens next. What you can control, however, is how you store your own passwords.
How should you store your passwords?
Obviously, saving them in a Microsoft Office document is not an option. It's way too risky, and the same goes for writing your passwords down on yellow pieces of paper and sticking them to your monitor. Hashing is out of the question as well. Even if you do have the tools and knowledge to do it, you need to be able to use your passwords.
Encryption, then, is your best bet. The data is not available in plain form, and yet, whenever you need it, you can use it.
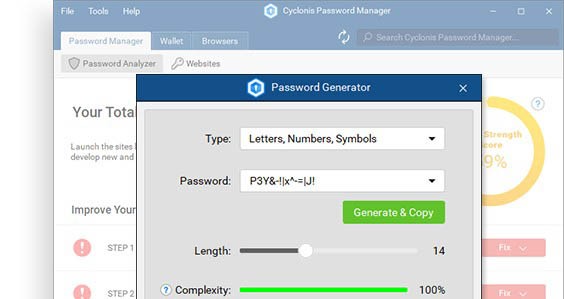
Cyclonis Password Manager gives you a convenient way of doing just that. First, it encrypts your data with AES-256, an encryption algorithm used by financial and military organizations from all around the world. Decryption is only possible with your master password, and since only you should be able to see your data, Cyclonis Password Manager won't store or transmit your master password in any way.
It's a having your cake and eating it scenario. Your passwords are kept well away from prying eyes, and yet, when you need them, you can use them. On top of it all, Cyclonis Password Manager is completely free.