Remove XMRLocker Ransomware

Ransomware creators do not often use Bitcoin to receive payments from their victims. Sometimes, they opt to go for more privacy-focused cryptocurrencies like, for example, Monero. This is the case with the XMRLocker Ransomware. Its creators ask for a ransom payment via Monero, and they promise to help every victim who agrees to pay the ransom fee. However, we would not advise you to try to fulfill the demands of the criminals. They may outright scam you or even decide to ask for more money once you make a payment.
Pirated Content May Hide the XMRLocker Ransomware
The XMRLocker Ransomware is often spread online with the help of fake downloads. Often, the malicious file may be me hiding inside a pirated application or game. This is why you should never interact with pirated content – it is a breeding ground for all sorts of modern malware.
When the XMRLocker Ransomware infiltrates a system, it will encrypt files it deems to be valuable. Typically, these are documents, media, archives, databases, backups, and similar data. After the damage is done, the XMRLocker Ransomware will mark the names of the files with the '.[XMRLocker]' extension. It then creates the ransom message 'ReadMe(HowToDecrypt).txt.'
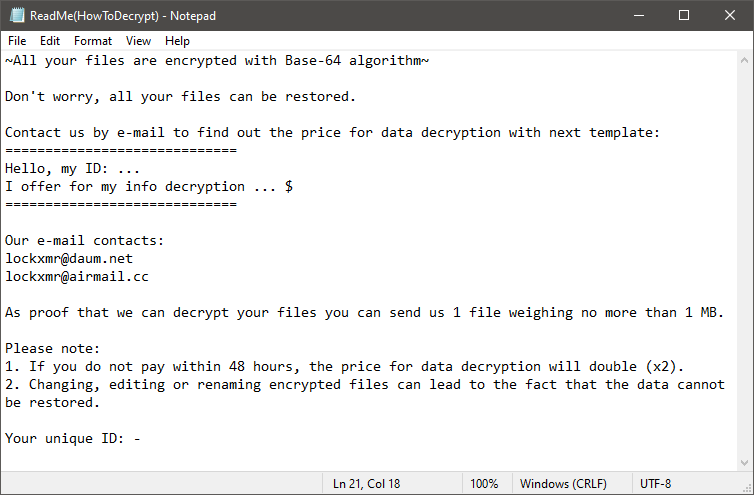
Surprisingly, the XMRLocker Ransomware also shows a fake Windows blue screen, which reads:
Does the morning starts with coffee?
All your files are encrypted by lockxmr@daum.net
We advise users not to consider paying the ransom fee that XMRLocker Ransomware's creators demand. Instead, they should run an anti-malware tool to eliminate the threat fully. After this, they can proceed to experiment with alternative data recovery software and methods. Keep in mind that this does not guarantee a full recovery. There is currently no free way to decrypt files that the XMRLocker Ransomware locks – only the creators of the threat claim to be in possession of a decryptor. However, they do not offer reliable proof that their decryptor works.








