Remove Temlo Ransomware

Ransomware attacks continue to be a profitable venture for cybercriminals. Many of thes hackers rely on custom-built ransomware, while others focus on using publicly available ransomware projects. One of the fairly new file-lockers to be discovered online is the Temlo Ransomware. It is part of the VoidCrypt Ransomware family, and its encryption is irreversible via free utilities. Victims of this attack may need to use alternative file recovery options. Unfortunately, those do not always deliver excellent results – the only way to guarantee a full recovery from the Temlo Ransomware attack is to restore from a backup.
Temlo Ransomware may reach systems and networks through various infection vectors. However, the criminals behind it usually focus on malicious email attachments to propagate the dangerous software. These files may be masked as harmless Microsoft Excel or Office documents. However, they pack a malicious macro, which the file can decrypt and execute to deploy the Temlo Ransomware.
Temlo Ransomware - Why You Should Not Pay
When this ransomware attacks, it quickly encrypts documents, media, archives, backups, databases, and other file formats. It then applies the extension '.[temloown@gmail.com][<VICTIM ID>].temlo' to files it locks. It is important to add that using a Gmail account is not typical for cybercriminals – this is likely an indicator that Temlo Ransomware's creators are amateurs. Their Gmail profile will probably be taken down in a matter of days, and their victims will not be able to get in touch with the attackers.
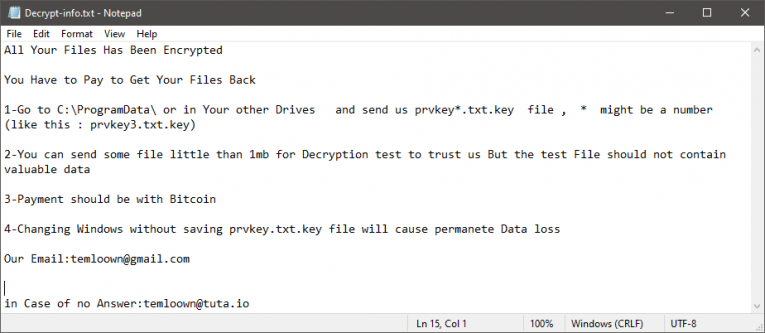
The Temlo Ransomware also drops the ransom message 'Decrypt-me.txt.' It explains the attack to the victim and instructs them to contact tmeloown@gmail.com or temloown@tuta.io for assistance. We advise you not to do this because the criminals request a ransom payment via Bitcoin. Trusting them and sending money is a bad idea – they are likely to scam you. The best way to proceed is to run an antivirus tool to eliminate the threat. However, you will still need to restore your files. In these cases, it is best to rely on alternative options like restoring from a backup or 3rd-party data recovery tools.