Remove Hudf Ransomware
The Hudf Ransomware is a slightly modified variant of the STOP/Djvu Ransomware, which has been plaguing Internet users for over three years. Unfortunately, there is no free decryption tool to assist victims of this threat. The STOP Ransomware is considered to be incompatible with free decryptors, and this is not changed for the Hudf Ransomware variant.
When this file-locker infiltrates a system successfully, it will immediately lock users out of their files. Every file it locks is marked with the suffix '.hudf.' in addition to this, users will also find the ransom document '_readme.txt' on their desktop, and in folders containing encrypted files. If you have not encountered ransomware before, then let us tell you what the hackers behind it usually want – your money. They offer to sell a decryption tool, which is supposed to help you get your data back. However, you should pay for it in Bitcoin, and there is usually no guarantee that you will get anything in return. Clearly, sending money to cybercriminals is risky – you should not do it.
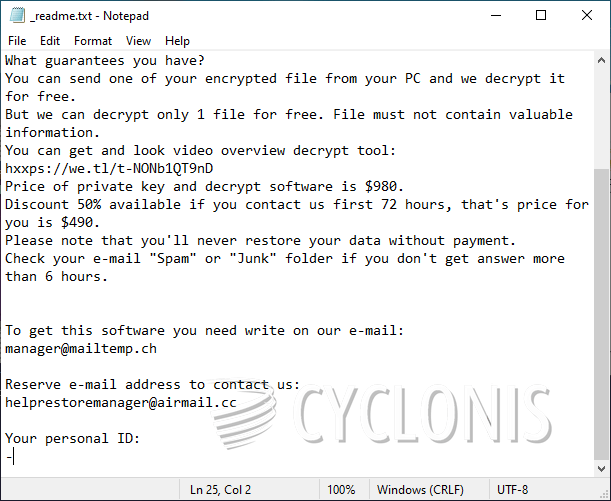
The Hudf Ransomware creators ask their victims for a $490 payment, and threaten to double it if the victim does not comply immediately. They also include an offer to unlock one file for free, and mention the emails manager@mailtemp.ch and helprestoremanager@airmail.cc for contact. Since trying to co-operate with the hackers is a bad idea, you should look for an alternative option. Our advice is to start by removing the threat by running an antivirus application. Then, try out reputable data recovery software and methods.








