Watch Out For Another Dropbox Phishing Email Titled 'Po.Pdf'
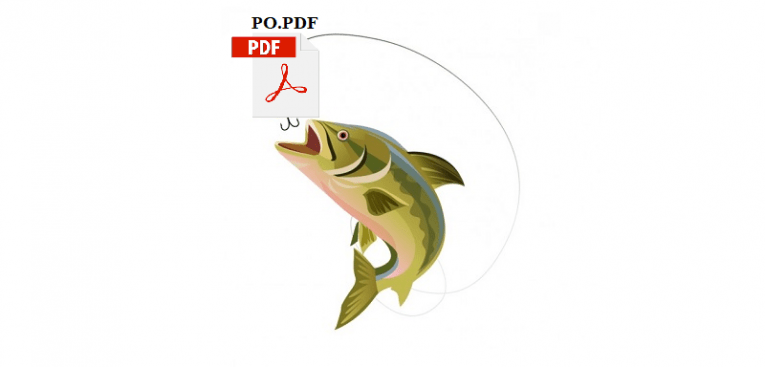
It is a sad fact of life that as the sophistication of the technologies available to us grows, so does the ingenuity and determination of bad actors to exploit and victimize regular users. Once upon a time, the efforts of malicious actors were easily discernable for anyone with an iota of knowledge on the subject of cybersecurity, and their depredations could be staved off by just following one or two pieces of good advice. Unfortunately, that's no longer the case – hackers nowadays are in the habit of using both sophisticated tools and high quality, multi-layered social engineering tricks and misdirection to scam their victims. Case in point – the recent Dropbox “PO.PDF” phishing attacks.
This particular campaign hit the web recently, and was pretty convoluted, as far as spoofs go. An email hit inboxes, with its main hook and the element that was supposed to lend it an air of legitimacy being a Dropbox logo. It had the appearance of an official notification from the file-sharing platform, which informed the recipient that a file titled "PO.PDF" was sent to them using Dropbox Transfer, and that this file will be accessible for just six days.
The email's goal is to trick users into clicking on the link to view a file, which would then lead them to a page hosted on the Dropbox domain. This page is very convincing, with high-quality branding elements and links to Dropbox support pages and everything.
Clicking on “Download” starts downloading a ".PDF" file that contains the Office 365 logo. A message that "a document has been sent through OneDrive" appears, and in order to access it, the user should click the "Access Document" button. This link then leads the user to a landing page hosted on Google Docs named "OneDrive". Here's where the actual phishing takes place, as users are asked to log in to OneDrive account and password to view the document.
Perceptive and knowledgeable internet users would have figured out that there is something wrong with this particular situation from the get-go. Firstly, this type of communication is highly atypical for Dropbox. Even in the event that the initial contact with the scam doesn't raise alarms, the fact that you have to jump through a bunch of hoops in order to access some file that the other party allegedly wants to send you should be a telltale sign that something's not right. Additionally, the fact that the file supposed to be shared via Dropbox, and in spite of this, you have to interact with two other platforms, like Office 365 and OneDrive, is a dead giveaway that something's wrong. Finally, the fact that you're asked to log in on an unverified landing page should be the last, glaring sign that you're being scammed.
In spite of the fact that all the signs are there and are clear for all to see, many users still fall for such obvious scams, and then end up paying dearly for that mistake. Here are some tips on what to do to avoid becoming the victim to a phishing scam:
How to Avoid Phishing Scams
- Always see if the sender's email address checks out. If someone claims to be contacting you from Dropbox Support, but if the email from which the message originates is clearly not dropbox support, the user is almost certainly the target of a phishing attempt.
- Note if the message starts with a generic greeting, or the user's email address or phone number is all wrong. No company ever starts their emails with "Dear customer" – only fraudsters ever do that.
- Be wary if the message contains any suspicious links – or any links that are platforms that you don't recognize on sight. If the email contains overly long, obfuscated links, chances are that they are going to take the user to some sort of phishing landing page.
- Be extra careful of unsolicited messages, especially those that contain an attachment of any sort. Never input any personal information, or enable macros, on files downloaded from such messages.