Schemers Employ a New Phishing Email to Collect Microsoft Passwords
Can you name the world's most lucrative type of cybercrime? Unfortunately, we can't definitively say whether or not your suggestion is correct. The world of online fraud is so vast and diverse that there simply is no way of saying for sure which particular scheme has generated the biggest losses. It's pretty safe to say, however, that Business Email Compromise (or BEC) is very near the top.
In July last year, FBI's Internet Crime Complain Center (IC3) came up with some interesting BEC statistics. According to its data, between October 2013 and May 2018, a total of $12.5 billion was fraudulently redirected thanks to BEC scams. During the same period, 41 thousand organizations lost in excess of $2.9 billion in the US alone.
It's a pretty serious problem that can have devastating consequences, especially for smaller businesses. The worst thing about it, however, is that, as a BEC campaign that started last week shows, the scam can be extremely easy to pull off.
Table of Contents
Short, quick, and to the point
The attack was first spotted by researchers from GreatHorn on January 31. The campaign is aimed at high-profile employees (CEOs, CTOs, SVPs, etc.) of a number of companies, and its ultimate goal is phishing the victims' Microsoft usernames and passwords. As is often the case, it all starts with an email.
The scammers are apparently using something called "direct spoofing" which, when we're talking about email, means using the same email address for both the "From" and the "To" fields. This could normally raise some eyebrows, but the body of the email might just be enough to convince the victim that the message is genuine. Every victim gets their own customized email, but the messages are intentionally made to look like they were automatically generated by a web application called Doodle.
The message tells victims that a management meeting has been rescheduled, and they are invited to click a link and vote on a new time and place for the important rendezvous. Doodle's is designed to help employees and managers keep track of meetings and appointments which makes the scenario sound plausible.
When they click the link, victims are led to a legitimate-looking login page that asks for their Microsoft login credentials. As you might have guessed, all usernames and passwords entered on the said page are automatically sent the crooks' way.
The potential damage is enormous
According to GreatHorn, we're talking about a massive campaign. As many as 14% of their customers were targeted, and we can only imagine how many more organizations received the fraudulent emails. Although a portion of the messages landed in the victims' Spam folders, the nature of the notifications probably convinced some people that this was a mistake.
Those that did unwittingly give their Microsoft login credentials to the crooks could be in for an unpleasant ride. Don't forget that we're talking about Top-Level management people in a corporate environment. If their business uses Microsoft's products extensively, their password can open the proverbial Pandora's box.
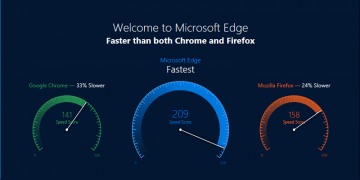
Although it still has a long way to go before it can reach Google's G-Suite, Office 365's market share is growing, and Microsoft's apps are tasked with handling and storing tons of sensitive data that can be stolen, abused, and held to ransom. Compromising it from the outside is difficult, but if you have the right password, getting to it could be as easy as pressing a few buttons.
This is hardly the perfect crime
On the one hand, the crooks' decision to use a Doodle-themed email to lure victims out of their Microsoft passwords seems like a clever move. On January 30, a day before the first messages were spotted, Doodle announced that it's adding a "Continue with Microsoft" button to its login page. In other words, logging into the calendar management tool using your Microsoft password became possible just hours before the crooks started sending the fake messages. There is one crucial difference, though.
If you really want to use Doodle with your Microsoft account, you first have to go to Doodle's login page, you then need to click "Continue with Microsoft", and after this, you will be asked for your login credentials if you're not logged in. By Contrast, the fake emails redirects targets directly to a Microsoft login page – a seemingly small discrepancy, but one that could save you plenty of headaches. If you notice that the URL is face before you give out your credentials, you should also be fine.
In the end, it all boils down to avoiding links in emails you weren't expecting and thinking twice before giving out any usernames and passwords. It should all be common sense, and lack of it can, as IC3's stats show, be rather expensive.