Remove Pooe Ransomware

The STOP/Djvu Ransomware continues to be one of the most prominent ransomware families in recent years. Hundreds of cybercriminals have used it to craft their very own ransomware projects and, unfortunately, this continues to this very day. One of the most recent variants of the STOP family is the Lssr Ransomware. Today's topic of discussion is another new variant, which goes by the name Pooe Ransomware.
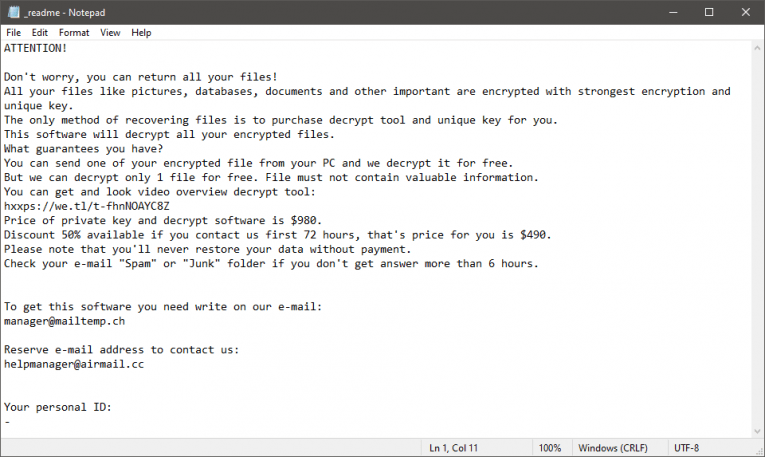
Unfortunately, the Pooe Ransomware's encryption is very secure, and there is no way to reverse it via free utilities. The criminals behind the attack claim to have a working decryptor, but they will only provide it to victims who pay a ransom fee. At least, this is what their ransom note, called '_readme.txt,' says.
Trusting ransomware operators is never a good idea because it is incredibly easy for them to scam their victims. For example, Pooe Ransomware's authors want to receive payments via Bitcoin. They ask for a fee of $490, but threaten to double the amount if the victim does not comply with their request within 72 hours of the attack. It is important to add that payments via Bitcoin are not reversible, and you might be unable to cancel or restore your transaction if Pooe Ransomware's authors do not fulfill their promise.
Spotting Pooe Ransomware's attack should be relatively easy. Unfortunately, once you see the consequences, there is little you can do to undo the damage. The best way to stay safe is to use an up-to-date anti-malware software at all times. On top of this, you should follow the best safe Web browsing practices. Avoid visiting torrent trackers, stay away from pirated content, and only download files from trustworthy source.
Victims of the Pooe Ransomware will find the '.pooe' extension at the end of the names of damaged files. The '_readme.txt' ransom note we mentioned above contains a short description of the attack, the amount of the ransom fee, and the emails which can be used to contact the attackers - manager@mailtemp.ch and helpmanager@airmail.cc.
Victims of this attack should not agree to send any money to the criminals. Instead, use an antivirus tool to clean off the infection. After this, experiment with reputable data recovery software to try and restore access to as many of your files as you can.







