Remove Moqs Ransomware

The STOP Ransomware continues to provide hackers with access to an easy-to-use file-locker. The latest file-locker to be crafted via the STOP project is called the Moqs Ransomware. It causes potentially irreversible damage to your data and then extorts you for money. The criminals claim that any victim can purchase a decryption tool and key in exchange for a payment through Bitcoin. Just like other variants of STOP, this one also starts by asking for a ransom fee of $490 – however, they threaten to double the ransom amount if the payment is not submitted on time. Other STOP variants following this strategy are the Ufwj Ransomware and the Gujd Ransomware.
The Moqs Ransomware's payload may be spread through spearphishing emails, pirated content, fake downloads, deceptive as, and other shady content. If the Moqs Ransomware's attack is successful, it adds the extension '.moqs' extension to the names of files it damages. It usually ends its attack with the creation of the '_readme.txt' ransom note.
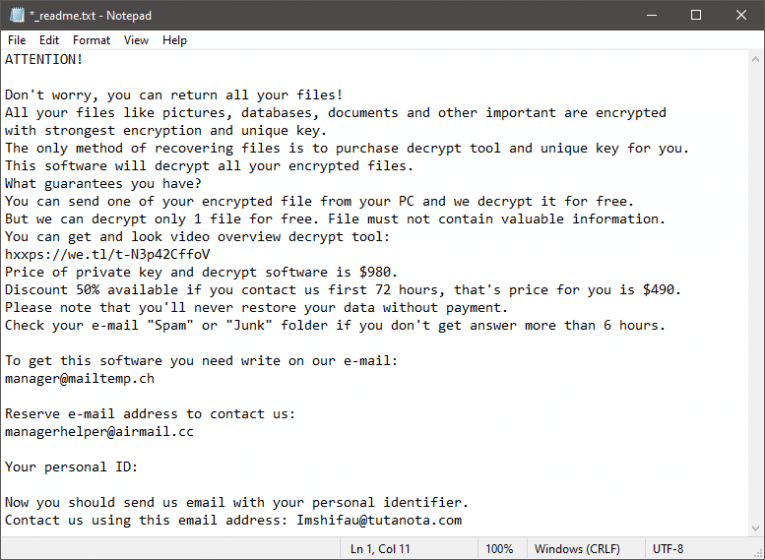
As we already mentioned, the document asks victims to pay a fee via Bitcoin. The criminals also offer to prove that their decryptor works by unlocking one small file for free. Victims are told to send the file they want decrypted to manager@mailtemp.ch or managerhelper@airmail.cc.
We advise you not to limit your interaction with Moqs Ransomware's creators – only ask them to decrypt that one small file. Paying the ransom fee is a terrible idea because the crooks might opt to scam you. Instead of trusting them, you should try to undo the damage via legitimate tools and methods. Start by running an antivirus tool to eliminate the Moqs Ransomware, and then look for alternative data recovery options.