Remove Hoop Ransomware

The Hoop Ransomware is a file-encryption Trojan belonging to the STOP/Djvu Ransomware family. Unfortunately, the latter is one of the most active projects at the moment. It is infecting hundreds of devices on a daily basis. The Hoop Ransomware is just the latest name that the affiliates of the STOP Ransomware gang use. Unfortunately, recovering from this attack can be very challenging and maybe even impossible if you do not have a backup copy of your data. Other variants of STOP that act in a similar manner include the Nooa Ransomware and Hhqa Ransomware.
How is the Hoop Ransomware Spread?
Threats like this one are often distributed with the help of pirated content. Many cracked applications and games might come with a hidden malicious file. We advise users to stay away from pirated downloads and to avoid downloading any content from torrent trackers – sites of this type are a breeding ground for dangerous malware.
However, pirated content is not the only trick that Hoop Ransomware's creators have up their sleeve. They may also target individuals, companies, and organizations via fake emails. These emails usually claim to come from a legitimate sender, and they urge the victim to download and review an attachment. The email usually presents the dangerous attachment as an invoice, document, or another relevant piece of information.
How to Spot the Attack?
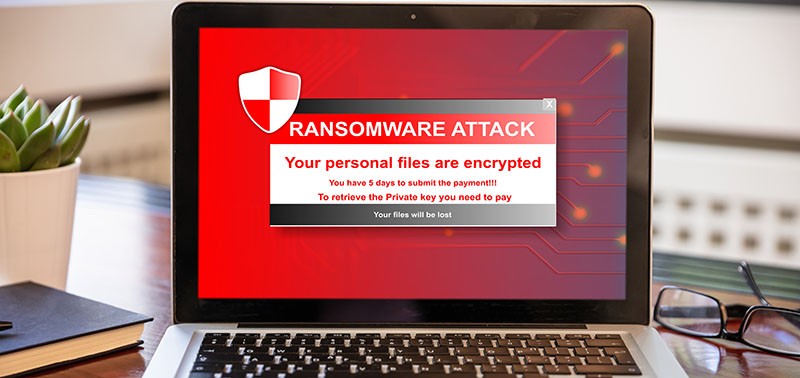
After this ransomware carries out its attack, it will encrypt important types of files. These files have the '.hoop' suffix added to their name. Victims will also find the ransom message '_readme.txt.' This document advises them to stay away from 3rd-party recovery methods because, allegedly, this may cause more damage to their files. The criminals promise to provide a working decryptor as soon as the victim agrees to pay a ransom fee of $980. They also ask the victim to contact them via helpteam@mail.ch or helpmanager@airmail.cc.
If you are one of Hoop Ransomware's unfortunate victims, then we advise you not to trust the attackers. They may not help you even if you comply with their demands. The suggestion of cybersecurity experts is to avoid co-operating with ransomware creators. Instead, use an antivirus scanner to terminate the malware and then explore alternative data recovery tools and options.