Remove Bopador Ransomware

File-encryption Trojans like the Bopador Ransomware have the ability to cause long-lasting damage to your data. Their attacks usually happen when you interact with a malicious file, and you do not have your system protected by antivirus software. The consequences of the attack usually involve inability to access your important media, documents, videos, and other content. The creators of the Bopador Ransomware may tell you that you can restore your files by purchasing a decryption tool from them. However, you should not believe their promises – sending them money is a terrible decision.
Victims of the Bopador Ransomware often encounter this malicious file while interacting with phishing emails, fake downloads, torrent trackers, or pirated content. Needless to say, you should stay away from untrustworthy websites, or pages used to spread shady content. Furthermore, investing in antivirus protection is the best way to counter threats like this one.
Do Not Trust the Bopador Ransomware Operators
The Bopador Ransomware is part of the STOP/Djvu Ransomware family, just like the Rigd Ransomware. Unfortunately, these ransomware variants are not decryptable. You will not have access to a free decryption software, and you should certainly not try to buy one from the criminals. The Bopador Ransomware marks the files it locks with the extension '.bopador' and drops the ransom note '_readme.txt.' According to this file, victims can ask for assistance by sending an email to gorentos@bitmessage.ch or gorentos@firemail.cc. Allegedly, the criminals also use the Telegram ID @datarestore.
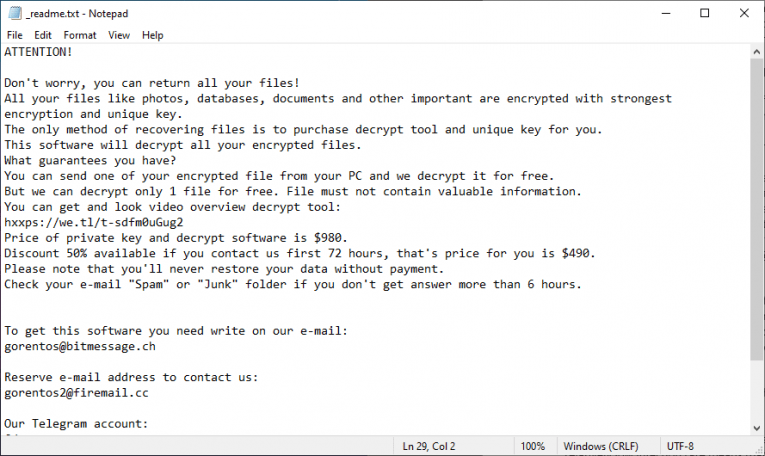
It is important to add that the crooks offer to unlock a single file for free. You should probably message them and try to get them to decrypt one of your files. Even if they fulfill their promise, you should still not consider paying the ransom fee. Do not forget that they want you to pay through Bitcoin, which would make it impossible to reverse the transaction. This makes it easy for them to scam you.
If you are a victim of this attack, you should use an antivirus scanner to eliminate the malware. After this, explore popular data recovery techniques, options, and software.