Remove 0xxx Ransomware

For the past couple of years, ransomware attacks have been a very profitable venture for cybercriminals of all ranks. Unfortunately, this trend is not dying down, and dozens of new file-encryption Trojans are being detected by antivirus tools every week. One of the newly identified threats is called the 0xxx Ransomware. It seems to be delivered to its victims through fake email messages, fake downloads, pirated content, torrent trackers, and other dubious files. It works just like popular ransomware families – it encrypts files, and then offers to sell a decryptor.
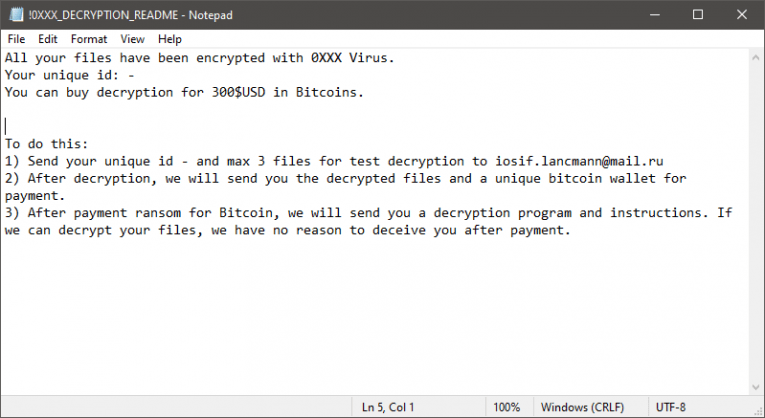
The 0xxx Ransomware's attack will render many important files inaccessible – archives, media, documents, and backups are just some of the popular types of files it encrypts. Once it locks a file successfully, the threat will apply the '.0xxx' extension to its name. Of course, the criminals also need a way to provide their victims with instructions on what to do. This happens via the file '!0XXX_DECRYPTION_README.txt' that the ransomware drops after completing its attack.
The 0xxx Ransomware is not Compatible with Free Decryptors
Unfortunately, these are not the only changes that the 0xxx Ransomware introduces. In order to make the recovery of the lost files next to impossible, the ransomware will try to wipe out Shadow Volume Copies, and disable the System Restore service. These two Windows components may sometimes enable users to restore some of their data for free – the 0xxx Ransomware makes sure that this does not happen.
Sadly, 0xxx Ransomware's encryption routine is very secure, and a free decryption tool is not available. However, we assure you that you should not consider paying the ransom fee that the criminals ask for. They ask for a payment of $300 via Bitcoin, and provide the email address iosif.lancmann@mail.ru for contact. Sending the money is not recommended since there is a high likeness that 0xxx Ransomware's creators will end up scamming you.
Instead of trusting anonymous ransomware operators, victims of this threat should seek alternative data recovery options. Before doing this, however, they should make sure to eliminate the infection. This can be done by running a reliable antivirus scanner and performing a full system scan.







