How Do You Know If You're Using a Pwned Password?
Users still use weak passwords despite specialists’ efforts to enlighten them on the importance of setting secure digital locks for all their accounts, so there is nothing surprising that the password hacking rate has not decreased by a single percentage point in the past few years. In fact, research has shown that the situation has even got worse. According to Verizon, the number of data breaches that involve pwned passwords has gone up from 50 percent to 81 percent during the last three years, which clearly shows that traditional security measures security experts recommend taking simply do not work or are not taken seriously even though 8 out of 10 users admit to be concerned about their online privacy and security.
Table of Contents
Why do passwords get pwned?
While some specialists blame websites and their developers for allowing users to set weak passwords that can be easily pwned, the majority of researchers agree that the end-user is, without a doubt, responsible for his/her security to a great extent too. Unfortunately, some users still fail to understand that using strong passwords can help shield against cyber attacks. They choose short “easy to type” passwords that can be remembered easily over complex ones, which automatically puts them at risk of a data breach. Recent research has shown that nearly 10 percent of all the users used passwords from the worst passwords list at least once, whereas 3 percent used 123456, which is considered one of the weakest passwords in the world since it can be pwned easily. It should be noted that substituting characters, such as numbers and special symbols, for letters does not dramatically increase the password strength even though it is one of the most popular pieces of advice regarding password security.
Sharing is not caring when we talk about passwords. A recent survey has shown that 41% of American adults using online services have shared their passwords with somebody else, typically, friends and family, so it is not surprising at all that so many passwords end up in hackers’ hands and get pwned. Remember, it is a bad practice to share passwords that unlock online accounts full of private information. There is nothing safe about keeping passwords listed in an unprotected text document on your computer too because they will get pwned in case cyber criminals gain access to your system. Last but not least, you should check the login form twice before entering your password to make sure you do not share your credentials with hackers.
There is one more reason why so many passwords are pwned these days – users still reuse passwords across multiple services. A survey of 2000 people living in the United States, Germany, Australia, France, and the UK has revealed shocking findings: 91% of respondents are well aware of the security risks associated with password reuse, but 59% do so anyway. If you ask us, it is a dangerous practice. You push yourself into danger by reusing passwords. Generally speaking, all your accounts might be hacked overnight if one of your accounts’ password is pwned.
How do I tell if my password has been pwned?
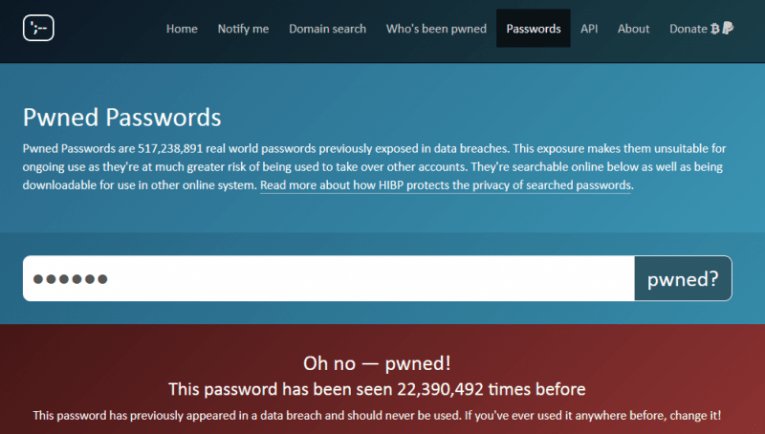
If you have detected suspicious activity on your online account, there is a possibility that your password has been pwned, i.e. you have become a victim of a data breach. Woah, do not freak out, it is not the end of the world. What we expect you to do instead is to access Have I Been Pwned. You will be asked to enter the password you are worried about (don’t worry, it is safe) and then click the pwned? button to check if it has been pwned.
The original database has recently received a massive update. While the initial version of the Pwned Passwords database consisted of 320 million hacked passwords taken from a variety of sources, the most recent version, usually referred to as Pwned Passwords V2, contains 501,636,842 leaked passwords collected from various data breaches. The database now also includes two major sources: Onliner Spambot Dump consisting of 711 million records and 1.4 billion clear text credentials discovered on the Dark Web. Some minor sources have been added to Pwned Passwords V2 too, making it even more reliable. On top of that, some junk records have been removed from the database, slightly reducing the size of Pwned Passwords V2.
I have been pwned. What do I do now?
If you get the message that you have been pwned, it would be a smart move to change the compromised password ASAP to avoid further security-related problems, especially if it is reused on multiple sites because you might find all your accounts hacked and information stolen from them in no time. Do not set a weak password that can be pwned easily again. Instead, choose a secure password cyber criminals could not crack.
What an ideal password looks like, you may ask. Well, first of all, you need to choose a password that is long enough. Security specialists say that a secure password must consist of 12 characters minimum, but it is, of course, advisable to go up. Second, it should contain a mix of numbers, symbols, and upper/lower-case letters. Third, it cannot be a simple word that can be found in a dictionary. A combination of several dictionary words is not considered a strong password too. Last but not least, you should refrain from using personal details (e.g. address) in your passwords as well because such passwords can be easily pwned.
Top 3 tactics used to pwn passwords
Phishing
Technically, fishing has nothing to do with fishing. It can be described as a type of a cyber attack whose primary goal is to trick users into providing sensitive information, including login credentials. One of the best phishing examples is fabricated emails with password recovery links opening fake portals. They are sent to Internet users around the globe seeking to obtain their logins and passwords and thus access their accounts. These phishing emails are so convincing that, according to Intel Security, 80% of people still fail to recognize them.
Brute force
Brute force is still considered one of the most popular password cracking methods. It is usually referred to as a trial-and-error method because an attacker tries all possible character combinations hoping to crack the password set. Needless to say, some passwords are easier to crack than others. It might take years to hack a secure password, whereas simple passwords like 123456 can be guessed within moments. This proves the importance of setting complex passwords for all accounts again.
Dictionary attack
It is an uncomplicated password hacking tactic. Why is it called a dictionary attack? Because it is all about trying words in a dictionary until a correct word used as a password is found. The so-called dictionary is not a book used in a classroom. Usually, it is a small file that also contains the most popular password combinations, e.g. 123456 and qwerty.
If it has turned out that your password has been pwned, you must reset it immediately. Creating a secure password that is hard to crack is a necessity in today’s world, so spend some time to come up with the best password for your account. If you are far from being an inventive person, you can use Cyclonis Password Manager to generate a secure password. It would also keep all your saved passwords encrypted in your personal vault and automatically enter them into login forms for you. We can assure you that none of your passwords will get pwned as long as you keep your master password granting access to the password manager safe.
Tip: You can estimate the total strength of all your saved passwords using the Password Analyzer feature of Cyclonis Password Manager.









It's an amazing article in favor of all the internet people; they will get benefit from it I am sure.