Bad Password Practices and How to Avoid Them

In 2004, during Microsoft's annual IT Forum, Bill Gates boldly announced that the password is dead. Normally, there aren't many people that will be willing to challenge his words, especially when he's talking about things related to computers. When he said that the password is about to meet its maker, however, he got it a bit wrong.
About fourteen years on, the password is still pretty much alive and kicking. In fact, it protects far more information now than it did back when Microsoft's co-founder predicted its demise. That includes our bank accounts, our email communication, our social networks, our favorite TV shows, our music – basically, our whole online life, and in some cases, a portion of our offline existence.
But is the password still ubiquitous because it's the perfect authentication mechanism that can't be improved upon? No. Not in the least. In fact, passwords have proven time and again that they're a poor way of protecting valuable information.
Don't take our word for it. According to Verizon's 2017 Data Breach Investigations Report, about 62% of 2016's data breaches involved hacking, and of them, more than 80% were related to weak and/or stolen passwords.
This, common sense dictates, means that passwords are far from ideal when it comes to verifying our identity on the Internet. Despite Bill Gates' predictions, however, we have yet to come up with an authentication system that's as widely adopted as passwords.
Ordinary users must accept that passwords are here to stay, and they must treat them with more respect than ever. The trouble is, as an infographic published by GCFLearnFree.org illustrates, few people get that.

Hal has gone down the easy route. He's probably pretty proud of his grandson, and he thinks about him every day. In that respect, using the small boy's name and age seems like a good way of avoiding the "Forgotten password" link. "CodyBanks8", the password he's chosen, has ten characters, with one digit and two uppercase letters. According to the zxcvbn algorithm, it has an entropy (a measurement of how unpredictable a password is) of around 23 bits, which is far from ideal. That's not the only problem, though. Being a proud and loving grandfather, Hal has also posted a picture of the small boy on his Instagram feed (yes, senior citizens use Instagram too), and he has written his grandson's name in the caption. This makes hackers' job (if you can call it that) quite a bit easier.
In the age of the social networks, it takes minimum effort to find massive troves of information about you and your loved ones on the Internet. Some people know how to keep their Facebook/Instagram/Twitter feeds private, but many don't, and even if your posts are shared with your friends only, this can't guarantee that you'll be safe.
In any case, you are the one who should decide whether anyone can see your social media activity. Just make sure that any attempts to guess your password based on it are unsuccessful.
We see pretty much the same story with Jarrod. His password, "ILuvFishing" is slightly longer than Hal's and it has a marginally better entropy (about 25 bits). This doesn't matter, however, because his profile depicts Jarrod practicing his favorite hobby, and hackers know that if your Facebook timeline is full of Metallica songs and pictures, then there's a great chance that your password would be "MetallicaRocks!". Users shouldn't stop sharing things that interest them on social networks. They should, however, stop using references to them in their passwords.
Bryan is aware of this. "BrAveZ!2" might be only eight characters long (not really an ideal length, it must be said), but it contains three uppercase letters, an exclamation mark, and a digit, which means that with an entropy of around 30 bits, it's harder to crack. The fact that the password isn't a name or a word that could be easily connected to him makes it difficult to guess as well. The problem is, passwords don't just get hacked or guessed. They also get stolen which is a problem for Bryan.
He has one password for all the websites he's using, and if one of the services gets compromised (and services get compromised every day), all his accounts are exposed. Exploiting reused passwords has been one of the easiest and most damaging ways of affecting users for a while, and in such a scenario, length and the use of special characters don't mean a thing. That said, passwords should never be simple. Case in point: Emilia.
"123abc123" has an entropy of just 6.4 bits which means that it can be brute-forced in no time. Hackers don't need to brute-force it, though. Many people use patterns like "123abc123" because they're easy to type and easy to remember. That's why, the most common passwords (which include "123456", "Password", "qwerty", etc.) are included in the password dictionaries hackers use when they're trying to compromise an account. Sometimes, it takes no more than a few attempts to break in.
None of the people examined so far practice good password hygiene, and it would be rather easy to condemn them for that. The truth is, however, without external help, human beings are simply not capable of managing their passwords in a secure way.
In 2007, Microsoft researchers found out that the average user has about 25 accounts that require passwords (most probably, this number is much higher now). With a bit of effort, you can probably create tens of different passwords that are impossible to guess (in some cases, just bashing the keyboard will do that), but you'll find it really hard to memorize them and remember which one goes where. A password manager, however, can do that for you.
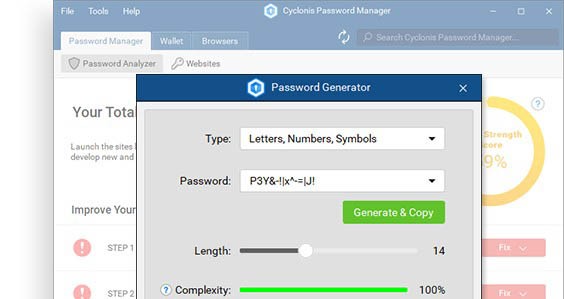
Jazmin is using a password manager which allows her to protect her online accounts properly. She has used the built-in password generator to create "m&t7T5$dAY" – a password that has an entropy of over 50 bits and is impossible to guess. The rest of her accounts can be protected by passwords that are just as strong, and best of all, she needn't worry about remembering or typing them because her password management application does that for her. In addition to better protecting her online identity, Jazmin also brings convenience that other users can never have without a password manager. It's a win-win if ever there was one.
Turns out that you, the regular Internet user, don't need to do anything to improve your passwords. It's better to leave it to the applications dedicated to doing just that.