What Are the Differences Between Cyber Security and Information Security?

Any user who encounters information technologies every single day will have dealt with information and cyber security in one way or the other. It basically means that every one of us is exposed to these security aspects. But it is probably very seldom that we think properly about these different types of security. In fact, sometimes even the specialists who work in the field are sure that cyber security and information security are synonyms, and you can't have one without the other. But if they were synonymous, why would you need two different terms? We are here to explain the differences between the two, and we hope you will find our post useful.
Table of Contents
What Is Information Security?
To understand what information security is, we have to first understand what exactly information is. After all, we always see things like "data security" and "information security," and it feels like information and data are used interchangeably. However, once again, they do not mean the same thing.
To put it simply, data may refer to any set of variables. It might be a string of numbers or a set of letters, but it does not necessarily have a meaning. Information, on the other hand, is data that HAS meaning. For instance, your birth date is a sequence of numbers, but it means something. So this is how we differentiate between data and information.
Consequently, we can encounter information anywhere. We can find it in analog sources (like books or notes on a wall) and digital sources (the Internet or your mobile device's memo app). So when we talk about information security, we mean all the methods and measures to protect confidentiality, integrity, and availability of all types of information, both analog and digital. Likewise, the methods you employ to protect a stack of books in the library will be slightly different from the things you do to ensure your social media account remains secure.
Perhaps it often seems that information security mainly deals with the aspects of cyber security because it is always at our fingertips when we browse the web, and the Internet is one of the main media that provides information access to a considerable number of users. Therefore, when we think "information security," we automatically associate it with the digital world. But it does not necessarily have to be like that.
What Is Cyber Security?
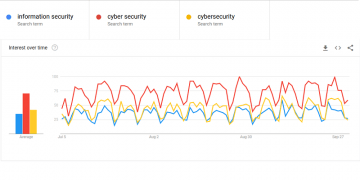
So while information security may refer to the analog and the digital spheres, cyber security clearly deals with the digital world. We can also see that cyber security is more relevant to netizens, too. If you check out the Google trends comparison below for "information security," "cyber security," and "cybersecurity" in the United States for the last three months, you will see that cyber security has been the more common search keyword.
So what is so special about cyber security? The point is that cyber security refers to every single method devised to protect anything vulnerable on the cyber space from being attacked, compromised or stolen. One of the things that can be stolen on the cyber space is, obviously, information. So if we are talking about the DIGITAL information, we could say that cyber security is part of information security. However, that's not all to it, and we shouldn't jump to such conclusions.
Let's think about it, is information the only thing that is present in the cyber space? The information would not be able to exist online without ICT (information and communications technology) and IT (information technology). In other words, we need software and hardware appliances to store the information and to access it. Consequently, software and hardware also become vulnerable to cyber threats, and so they fall under the scope of cyber security.
If we were to give you an example of something that is not information, but is part of the cyber security, we could point out network security. Network security is designed to prevent unauthorized access, modification, misuse, and other unsolicited activities on a computer network. Although a network by itself is not information, it is a medium that allows us to share the information and to access it. If we do not have that medium, it is impossible for us to use the information we need. Hence, network security is there to protect that medium.
What's more, we are sure that you are very well acquainted with cyber security even if you are not aware of that. You probably encounter things like antispyware software, firewalls, two-factor authentication, encryption, passwords, and other cyber security tools every single day. And since we use those tools to protect our digital information, it is easy to think that information security IS cyber security.
Cyber Security vs. Information Security
So what have we found so far? Perhaps our subtitle for the last part of our post is a little bit misleading. Technically, it is not cyber security vs. information security. They DO overlap when we deal with digital information, but the terms themselves refer to far broader scopes of application, and we just have to remember that digital space or information alone are not the limits.
To sum up, information security deals with methods that protect both analog and digital information from malicious exploitation, theft and so on. Whereas cyber security is a set of methods to protect digital information and other vulnerable things that are part of the cyber sphere. Both terms overlap when we talk about the digital information security. But your secret notes in your notebook scribbled with your favorite pen would not be governed by cyber security. And information security has nothing to do with securing your computer network or your hardware.
Perhaps it would make more sense to say cyber information security when we talk about protecting digital information, but it is very doubtful whether a regular user would ever feel the difference. As long as they keep an eye on their notes and use strong passwords and password managers for their social media accounts, we can be sure that they have their information and cyber security covered.









First time I notice an article that cleary outlines the differences between both concepts!Tx