Remove Koom Ransomware

File-encryption Trojans are designed to cause long-lasting damage to files. They do this by applying strong encryption to the contents of files, which is only reversible through the use of a special decryptor and key. One of 2021's prominent file-locker families is the STOP/Djvu Ransomware.
The Koom Ransomware is a successor to the recent Lqqw Ransomware, Efdc Ransomware, and other versions of the STOP/Djvu family. These viruses may be transmitted via one of the following ways:
- Fake download of a game crack.
- Fake software activators that are used to run pirated copies.
- Phishing emails containing a malicious attachment.
- Torrent trackers and other sources of pirated content.
Once the Koom Ransomware starts encrypting your files, they will be scanned based on their file extensions to determine which file types are to become encrypted. The most common file types are the following - documents (spreadsheets, presentations,) media (music, movies, photos,) archives (backups,) and videos.
Koom Ransomware Creators Demand Money from their Victims
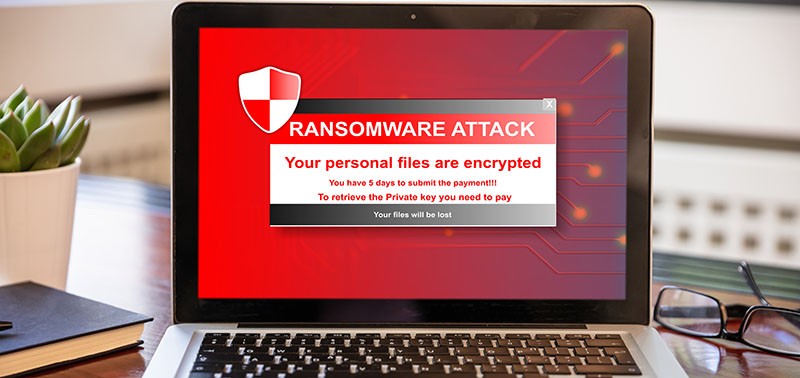
The Koom Ransomware is a type of malware that infects computers silently and blocks access to the computer or encrypts files. Some types of malware use sophisticated encryption algorithms to block access to the computer or to encrypt files. The goal of such malware is to force you to pay a ransom to regain access to your files.
Typically, files encrypted by ransomware can only be decrypted using a program or decryption key that only the attackers have. Victims can avoid paying the ransom if they have their backup files or a free decryption program is available online. A ransom should not ever be paid. The attackers may not send a decryptor even after the payment. They may simply delete your files. The attackers deliver a ransom note through the '_readme.txt' file. They ask for $490 via BTC, and advise the user to contact them at manager@mailtemp.ch and managerhelper@airmail.cc.
Ransomware should be removed from the infected computer as quickly as possible. It may cause more damage by continuing to encrypt new files and/or infect other computers on the local network, even after removal.