Remove Gray Hat Ransomware
The Gray Hat Ransomware, or the CLAY Ransomware, is a new and dangerous file-encryption Trojan. This type of malware has the ability to encrypt the files of the victim and then extort them for money. Unfortunately, these attacks can be very destructive – the Gray Hat Ransomware can encrypt hundreds of file types. After it encrypts a file, the ransomware will also add a new suffix to its original name. This is something that ransomware often does to mark files and make them recognizable. In this case, the ransomware's authors use the extension '.clay' to mark the files they lock.
Victims of this ransomware may not have many recovery options to use. The only way to reliably restore the lost files is through a backup, but this might not be available to all users. If you do not have a backup copy of your data, you may need to look for alternative options. Some popular data recovery software and tools may be able to help to undo some of the damage that the file-locker causes. However, they are rarely able to make a full recovery.
Gray Hat Ransomware Authors Ask for $500
The authors of the Gray Hat Ransomware claim to have a 100% working decryptor. However, they want you to pay for it – 0.01 Bitcoin, or approximately $500. We advise you not to accept their offer because you will probably lose your money. Ransomware creators are certainly not known for their honesty, and it would not be a surprise if Gray Hat Ransomware's operators scam their victims. The Gray Hat Ransomware displays a full ransom message thanks to the file '___RECOVER__FILES__.clay.txt' that it drops on the desktop. This file also mentions the number of files that the ransomware has encrypted, as well as the email to contact the perpetrators – clay_whoami_1@protonmail.ch.
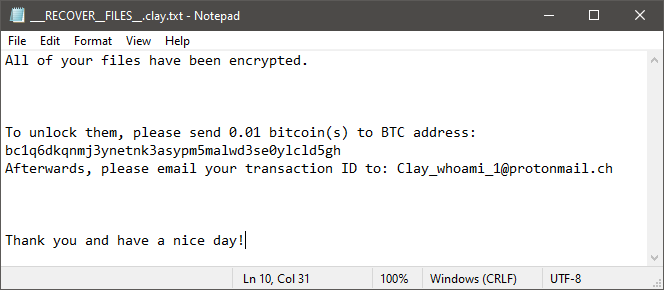
Our suggestion is to ignore the offer of the criminals. $500 is a lot of money to send to anonymous hackers who can scam you with ease. The best option is to run an anti-malware application to eliminate the threat. This will not recover your data, but it will stop the malicious program from causing more mayhem. After this, you can start experimenting with various data recovery tools and options.