ElonMuskIsGreedy Ransomware Is Greedy For Your Money

Ransomware attacks are becoming increasingly sophisticated, with cyber criminals using various themes and tricks to trap victims. One such threat making rounds is the ElonMuskIsGreedy Ransomware, a cleverly named malicious program designed to encrypt victims' data and ask payment for its release. While the name might draw some attention, the consequences of falling victim to this attack are serious.
Table of Contents
What Is ElonMuskIsGreedy Ransomware?
ElonMuskIsGreedy is a ransomware strain designed to encrypt files on the infected system, effectively locking users out of their data. However, ElonMuskIsGreedy Ransomware adds a unique touch by appending an elaborate extension to each encrypted file, which includes the victim's unique ID. For example, a file like "photo.jpg" would be renamed to "photo.jpg.ELONMUSKISGREEDY-[victim's_ID]," making it instantly recognizable as compromised.
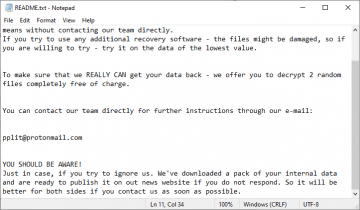
This ransomware also leaves behind a ransom note titled "README_SOLVETHIS.txt" to instruct victims on how to pay for their files' decryption. The message is clear: do not rename the encrypted files or attempt third-party decryption tools, as these could lead to permanent data loss. Interestingly, the note offers a discount to victims who contact the attackers within 24 hours, creating urgency and pushing victims toward paying the ransom.
Check out the ransom note below:
Hi!
Have a troubles?
Your personal ID: -
We will solve your problem but you need to pay to get your files back
I will show you all possible proofs before payment
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software - it may cause permanent data loss.
We are always ready to cooperate and find the best way to solve your problem.
If you write in 24h you will have a good discount
Write us
1)Session Private Messenger
You can download it to chat with us
On your server,pc or laptop - getsession.org/download
Install it and press PLUS
Write new message
Put there my SESSION ID
0568a6df0e0cecd44aee201a1c3c871be786013afa00bae1ed00b704d98d2a9215
Also you can install this messenger on your phone
SESSION at GOOGLE PLAY/APPSTORE
Install it and add me 0568a6df0e0cecd44aee201a1c3c871be786013afa00bae1ed00b704d98d2a9215
2) TOX messenger (fast and anonymous)
hxxps://tox.chat/download.html
Install qtox
Press sign up
Create your own name
Press plus
Put there our tox ID:
E9164A982410EFAEBC451C1D5629A2CBB75DBB6BCDBD6D2BA94F4D0A7B0B616F911496E469FB
And add me/write message
3)Jami messenger (Fastest and anonymous)
hxxps://jami.net/
Also you can find it on your phone at google play/app store
Install it on your server,phone or tablet
Press sign up and do your own nickname
And add me/write message - Decryptionguy (use search)
What Do Ransomware Programs Do?
Ransomware, like ElonMuskIsGreedy, works by encrypting the data on a target device, making it impossible for the victim to access or use their files without a decryption key. The key is held by the attackers, who demand payment—typically in cryptocurrency—to release it. Victims are often warned not to tamper with the encrypted files or seek help from outside sources, as any missteps could lead to irreversible damage.
Ransomware is not just a simple nuisance; it can cause extensive financial and operational damage to individuals and organizations. The most common way ransomware infiltrates a system is through phishing emails, where users are tricked into clicking on a malicious link or downloading a harmful attachment. In the case of ElonMuskIsGreedy, the attackers use specialized messaging apps like Session, TOX, and Jami to communicate with victims, providing a more anonymous and secure method of interaction.
What Does ElonMuskIsGreedy Ransomware Want?
Like most ransomware variants, ElonMuskIsGreedy's primary goal is financial gain. The ransom note demands payment in cryptocurrency, a common method used by cybercriminals to avoid being traced. Victims who fail to pay within the 24-hour "discount" window may face higher ransom demands or risk losing their data entirely.
Unfortunately, paying the ransom does not guarantee file recovery. Many victims end up paying without receiving the promised decryption tools, as cybercriminals have no obligation to follow through on their promises. This is why experts strongly advise against paying ransoms, as it not only funds illegal activities but also provides no guarantee of restoring access to compromised data.
How Can Ransomware Like ElonMuskIsGreedy Spread?
Ransomware spreads through various deceptive methods. One of the most common ways is through phishing emails, which trick users into downloading malware by clicking on a malicious link or opening an attachment. Other methods include drive-by downloads from compromised websites, fake software updates, and even technical support scams. ElonMuskIsGreedy can also be delivered via pirated software, cracking tools, and key generators, all of which are popular avenues for distributing malware.
Another dangerous aspect of ransomware is its potential to spread across a network. Once one device is infected, ransomware can quickly propagate to other machines on the same local network, causing widespread damage. This makes it crucial for businesses and individuals alike to act swiftly to remove the ransomware from their systems and prevent further harm.
Protecting Against ElonMuskIsGreedy Ransomware
While ransomware attacks are on the rise, users can take several steps to reduce their risk of infection. One of the most important precautions is to avoid downloading pirated software, cracking tools, or key generators. These files are frequently used as vehicles for distributing ransomware. Always download software and updates from official websites or trusted app stores to ensure authenticity and security.
Being cautious when browsing the web is equally important. Malicious advertisements, suspicious pop-ups, and deceptive download buttons are all common tricks used by attackers to lure users into downloading ransomware. Additionally, attachments and links in unexpected or unsolicited emails from unknown sources should never be opened without thorough inspection.
Backup Strategies Are Key
The most reliable way to recover from a ransomware attack without paying the ransom is by having backups of your data. Regularly backing up critical files to offline storage devices or secure cloud services ensures that, even in the event of an attack, you can retrieve your data without relying on the attackers' demands. Remember to keep these backups disconnected from your main systems when not in use, as ransomware can target any connected drives or network storage during an attack.
Moreover, ensuring that your operating systems and software are up to date with the latest security patches can help reduce the risk of ransomware infection. Attackers often exploit vulnerabilities in outdated systems, so keeping your devices updated is a critical defense against cyber threats.
Bottom Line
ElonMuskIsGreedy Ransomware reminds us of the evolving nature of cybercrime and the financial motivations that drive it. By encrypting victims' files and demanding payment for decryption, ransomware like this poses a significant threat to both individuals and businesses. However, with the right precautions—such as backing up data, being cautious online, and avoiding suspicious downloads—you can reduce the risk of such an attack. Stay vigilant, informed, and always be prepared to protect your data from ransomware threats.