What is the Dispout Trojan?
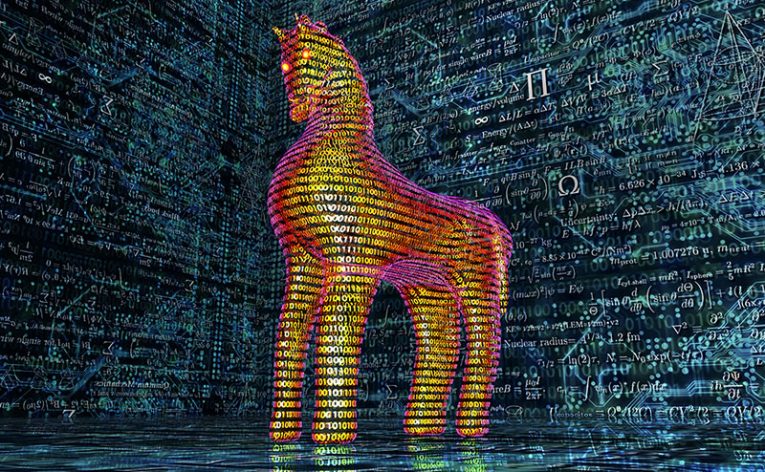
Trojan malware is a highly perilous form of malicious software that frequently masquerades as legitimate or harmless files or programs, aiming to deceive users and attain unauthorized entry into their systems. Despite its seemingly harmless façade, Trojan malware conducts malicious activities behind the scenes. Dispout is an example of such a threat that has been identified by information security researchers.
The malicious Trojan identified by researchers may be attempting to spoof an application with the same name.
Once it infiltrates a victim's device, this Trojan has the capability to carry out various harmful actions, including the illicit acquisition of sensitive information, undermining the security of the system, granting unauthorized remote access, or enabling the installation of supplementary malware.
Table of Contents
How Can a Trojan Get Inside Your System?
Trojans can infiltrate your system through various means and deceptive tactics. Here are some common methods by which a Trojan can get inside your system:
Email Attachments: Trojans may be disguised as email attachments, often sent through phishing emails. Opening these attachments can unknowingly trigger the installation of the Trojan onto your system.
Software Downloads: Trojans can be bundled with seemingly legitimate software or files that you download from the internet. When you install the desired program, the Trojan gets installed alongside it without your knowledge.
Infected Websites: Visiting compromised or malicious websites can expose your system to Trojans. These websites may exploit vulnerabilities in your web browser or use deceptive techniques to trick you into downloading and executing the Trojan.
Social Engineering: Trojans can also be delivered through social engineering techniques. Cybercriminals may employ tactics such as fake software updates, enticing downloads, or enticing advertisements to lure you into clicking on links or downloading infected files.
P2P File Sharing: Downloading files through peer-to-peer (P2P) networks can put your system at risk. Trojans can be disguised as popular files or software within these networks, and downloading them can lead to unintended Trojan installations.
Exploiting Software Vulnerabilities: Trojans can exploit vulnerabilities in outdated or unpatched software. By exploiting these security weaknesses, they can gain unauthorized access to your system and install themselves without your consent.
What Capabilities do Trojans Commonly have?
Trojans possess a range of capabilities that enable them to carry out malicious activities on compromised systems. Here are some common capabilities that Trojans commonly exhibit:
- Backdoor Access: Trojans often create a backdoor, providing unauthorized remote access to the attacker. This allows them to control the compromised system, execute commands, and potentially install additional malware.
- Data Theft: Trojans can be designed to steal sensitive information from the infected system. They may target passwords, login credentials, financial data, personal information, or other valuable data that can be exploited for various malicious purposes.
- System Modification: Trojans have the ability to modify system settings, registry entries, or configuration files to achieve their goals. They can alter security settings, disable or manipulate antivirus software, or modify network configurations to facilitate unauthorized access or maintain persistence on the compromised system.
- Keylogging and Screen Capture: Some Trojans are equipped with keylogging capabilities, which enable them to record keystrokes entered by the user. This can capture sensitive information such as passwords, credit card details, or confidential messages. Additionally, Trojans may capture screenshots of the user's screen, providing the attacker with visual information.
- Botnet Participation: Trojans can join a botnet, which is a network of compromised computers controlled by a central command-and-control server. By becoming part of a botnet, Trojans can be used to carry out coordinated attacks, distribute spam, conduct distributed denial-of-service (DDoS) attacks, or engage in other malicious activities.








