What Is Juice Jacking? Is It Safe to Use Public USB Ports?
You're in a public place, you need to use your smartphone, but you've forgotten to charge it up before you left home. You don't have a charger, and you've never really grown used to carrying bulky power banks with you.
You're far from the only one who's been in this situation. In fact, the need to charge mobile devices on the go has been so huge, that there are now thousands of free public charging points in places like airports and shopping centers. It's a twenty-first-century solution to a twenty-first-century problem, but in November 2019, the Los Angeles County District Attorney's Office said that using public charging points might not be such a good idea. Let's see why.
Table of Contents
What are the dangers associated with public charging stations?
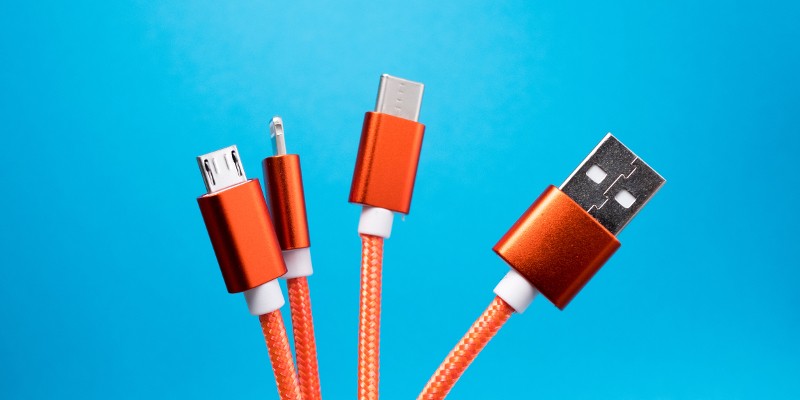
LA's District Attorney apparently wanted to educate people about the threat of juice jacking. As the name suggests, the concept entails compromising a device while it's being charged, and it exists because modern smartphones and tablets use the same ports and cables for both topping up the battery and transferring data. You all know that in addition to plugging your smartphone into an electrical outlet, you can also connect it to your computer and upload and download files to it while you are charging it. In a juice jacking scenario, cybercriminals hide a computer inside a public charging point, and when random people plug their smartphones in order to charge them, an automated script either steals data from the connected devices or installs malware on them.
We store massive amounts of sensitive information on our mobile devices nowadays, and juice jacking is just one of the ways of stealing it. But how does it stack up against the rest of the data-theft techniques?
Is juice jacking a legitimate threat?
The danger of juice jacking was first demonstrated during the 2011 DefCon conference held in Las Vegas. Back then, researchers from Aires Security installed a free public charging kiosk at the conference's venue and set up a small screen that invited passers-by to use it. According to Brian Krebs, no fewer than 360 attendees took advantage of the free electricity, but when they plugged in their devices, the screen told them how trusting random charging points could lead to data theft of a malware infection.
The researchers' goal was to raise awareness around the problem. Before setting up the public charging point, they did some experiments and found out that while mobile operating systems did have mechanisms for preventing surreptitious transferring of files, they didn't always work as expected. Their initiative showed that even hackers and people interested in information security didn't take the threat seriously enough.
Things have changed quite a bit since then. Over the years, we've seen other security experts demonstrate newer juice jacking techniques, and we're happy to say that operating system vendors have included more robust protection mechanisms.
How likely are you to become a victim of juice jacking?
Juice jacking is more difficult nowadays. The protection mechanisms mentioned above mean that secretly uploading or downloading data to a mobile device would involve an exploit of the operating system, which requires a high level of sophistication and a lot of resources.
In theory, the hard work could be well worth it for the hackers. The DefCon experiment showed that a single charging cable can affect quite a few people. In reality, however, while there have been plenty of Proof-of-Concept scenarios over the years, we have yet to see an in-the-wild attack with a significant impact. It looks like the hackers aren't willing to organize such a sophisticated operation without the assurance that their targets are valuable enough.
Juice jacking is a real threat, and it should not be ignored as a simple theoretical concept. Plugging in your mobile phone in a random public charging point does carry a certain level of risk, but you shouldn't forget that cybercriminals have a number of other, more widely used methods for stealing your data and infecting your device with malware.








