Suspected Malware-as-a-Service, RATDispenser, Delivers Trojans
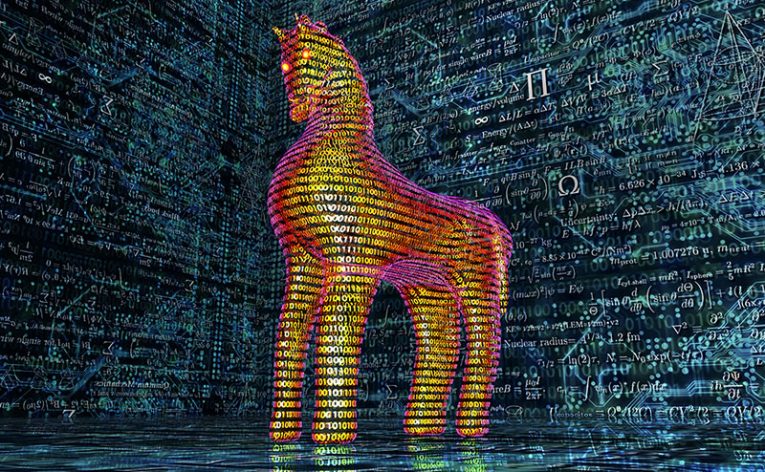
Typically Trojan Loaders focus on deploying one or two implants to the systems they compromise. However, what if there is a loader that is capable of unloading a wide range of payloads, depending on the attacker's needs? This is the case of the RATDispenser, a JavaScript-based loader, which carries a long list of Remote Access Trojan (RAT) payloads. In addition to delivering a wide range of implants, the RATDispenser is also able to evade built-in Windows security features.
Cybersecurity experts suspect that the RATDispenser might be offered as a service to cybercriminals who are willing to pay. One of the main reasons for this is the wide range of payloads it has been working it, and the fact that they appear to be all over the place – some are free, others are paid, and there are also custom-built ones. Some of the notable RATs that the RATDispenser has been delivering are STRRAT, WSHRAT, AdWind, FormBook, and Remcos. In some attacks, criminals were able to plant the Panda Stealer as well.
The JavaScript Loader was often spread with the assistance of phishing email messages, but it is likely that the operators of the RATDispenser were exploring other malware delivery mechanisms as well.
Protecting yourself from such attacks requires the use of an up-to-date antivirus software suite, and also knowledge on how to browse the Web in a safe manner. Stay away from non-trustworthy download sources, pirated content, and other suspicious files.







