Trojan:Script/Wacatac.H!ml Malware Detection
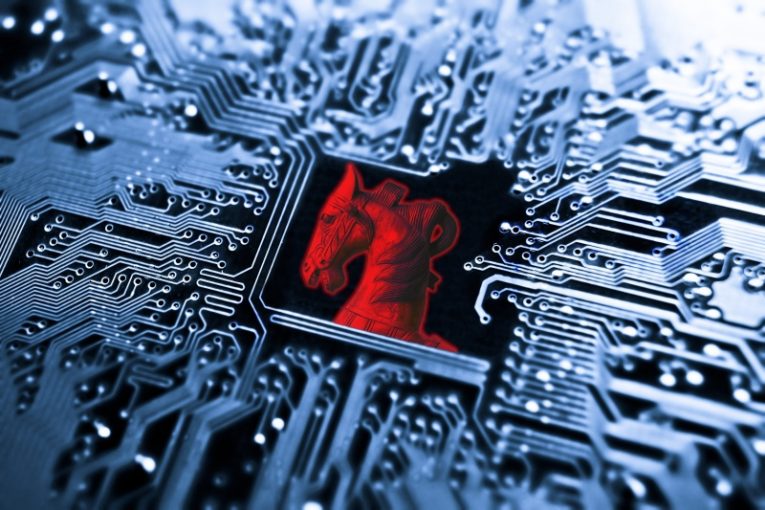
Our team has recently received requests for assistance from a number of web users who have fallen victim to a Trojan known as Trojan Script/Wacatac.h!ml. This particular Trojan is one of the latest versions of malware created by cybercriminals, and it has been causing significant problems for those who have been infected.
Trojans are among the most dangerous types of malware as they are incredibly stealthy and can be found in large numbers on the internet. In fact, Trojan representatives make up nearly 70 percent or more of all malware programs on the web, making them very common. If you have discovered that your system has been infected by Trojan Script/Wacatac.h!ml, you should consider running a full scan with a reliable and up-to-date anti-malware application.
What is a Trojan and How Can it Infect Your System?
A Trojan is a type of malware that disguises itself as a legitimate program or software, but once installed on a computer, it allows cybercriminals to take control of the system. Trojans can be used to steal personal information, damage files, or even take over the entire system.
Trojans can infect a system in various ways, such as through malicious email attachments, drive-by downloads, or software vulnerabilities. They often rely on social engineering tactics to trick users into downloading and installing them. For example, a Trojan may be disguised as a free antivirus program, a video player, or even a fake software update. Once the Trojan is executed, it may silently install other malware or open a backdoor for attackers to access the system remotely.
To protect your system from Trojans, it is essential to use reputable antivirus software and keep it up-to-date. Be cautious when downloading and installing software from the internet, and only download from trusted sources. Avoid clicking on suspicious links or opening email attachments from unknown senders. Additionally, regularly backup your data to prevent the loss of important files in case of a Trojan attack.
What Are False Positives in Malware Detections?
False positives in malware detections occur when a security program identifies a file or program as malicious or infected with malware, but in reality, the file is harmless and not infected with any malware. This can happen due to various reasons, such as an error in the detection algorithm, a misconfiguration of the software, or the presence of similar code or behavior to known malware.
False positives can be frustrating for users and can lead to unnecessary actions, such as quarantining or deleting harmless files or programs. It can also lead to a loss of productivity, as users may spend time resolving the false positive instead of focusing on their work. Therefore, it is important to regularly review and update the malware detection algorithms to reduce the occurrence of false positives.







