Danger Ransomware Is Definitely More Than Simply Dangerous

Table of Contents
Understanding Danger Ransomware
Danger Ransomware is a file-encrypting threat identified as part of the GlobeImposter family. Once activated, it targets stored data, rendering it inaccessible by applying encryption. This process involves modifying filenames by appending the ".danger" extension, indicating that the files are locked. Additionally, a ransom note is generated in a file named "HOW_TO_BACK_FILES.html," which gives victims with instructions on how to restore access to their files.
Ransomware like Danger primarily operates to force victims into paying a ransom. Cybercriminals behind these campaigns claim that decryption is impossible without their assistance, often leveraging fear tactics to increase the likelihood of payment. Victims are warned against attempting to restore files independently, as attackers allege that unauthorized recovery methods could lead to permanent data loss.
The Demands Behind the Attack
The ransom note associated with Danger Ransomware tells victims that their files have been encrypted using RSA and AES encryption algorithms, techniques widely used in securing sensitive data. The attackers claim that they are the sole holders of the decryption key, and any third-party tools or methods could corrupt the locked files beyond repair.
Beyond file encryption, the ransom note also includes an alarming claim that personal data has been extracted and stored on a private server controlled by the attackers. They threaten to destroy this data only if the ransom is paid; otherwise, they warn that the stolen information could be leaked or sold. This additional layer of extortion places further pressure on victims, increasing the stakes of non-compliance. The ransom note provides email addresses (pomocit02@kanzensei.top and pomocit02@surakshaguardian.com) and a Tor-based contact website, urging victims to respond within 72 hours to avoid a potential price increase.
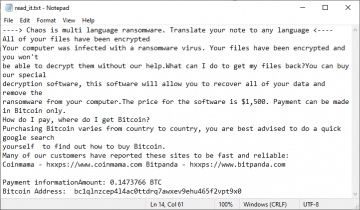
Here's what the ransom note says:
YOUR PERSONAL ID:
-
/!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\
All your important files have been encrypted!Your files are safe! Only modified. (RSA+AES)
ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE
WILL PERMANENTLY CORRUPT IT.
DO NOT MODIFY ENCRYPTED FILES.
DO NOT RENAME ENCRYPTED FILES.No software available on internet can help you. We are the only ones able to
solve your problem.We gathered highly confidential/personal data. These data are currently stored on
a private server. This server will be immediately destroyed after your payment.
If you decide to not pay, we will release your data to public or re-seller.
So you can expect your data to be publicly available in the near future..We only seek money and our goal is not to damage your reputation or prevent
your business from running.You will can send us 2-3 non-important files and we will decrypt it for free
to prove we are able to give your files back.Contact us for price and get decryption software.
email:
pomocit02@kanzensei.top
pomocit02@surakshaguardian.com
* To contact us, create a new free email account on the site: protonmail.com
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.* Tor-chat to always be in touch:
-
The Challenges of File Recovery
For most ransomware infections, retrieving encrypted files without paying the demanded sum is difficult. Since the attackers typically control othe nly working decryption keys, victims are left with limited options. Although some cybersecurity researchers have been able to develop free decryption tools for specific ransomware families, such solutions are not always available.
Maintaining data backups is a critical safeguard against such threats. If files are backed up before encryption occurs, users can restore them without needing to comply with the attackers' demands. However, if backups are stored on the same system, they may also become compromised. Furthermore, paying the ransom is not a guaranteed solution, as cybercriminals may fail to provide decryption tools even after receiving payment.
How Ransomware Spreads
Cybercriminals use various distribution methods to spread ransomware, such as Danger. One common approach is through pirated software and hacking tools, which often contain hidden payloads designed to infect unsuspecting users' systems. Additionally, ransomware is frequently distributed via deceptive emails that include malicious attachments or links. These emails may appear to be from legitimate sources, tricking recipients into opening harmful files.
Beyond email-based tactics, ransomware operators exploit technical vulnerabilities, fraudulent advertisements, and compromised websites to deliver their malicious payloads. In some cases, attackers leverage peer-to-peer networks and infected USB drives to spread ransomware across multiple devices. Once inside a system, some ransomware variants are capable of moving laterally within a network, affecting additional machines.
Final Thoughts
The most effective way to protect against ransomware is by adopting proactive security measures. Users should regularly update their operating systems and applications to patch known vulnerabilities that attackers may exploit. Security software should also be kept up to date to detect and prevent ransomware attacks before they can execute.
Additionally, individuals and organizations must exercise caution when handling email attachments and links, especially if they come from unknown or unexpected sources. Downloading software exclusively from official websites and trusted platforms further reduces the risk of inadvertently installing ransomware-laced programs.
By staying informed about ransomware tactics and implementing strong security practices, users can minimize their exposure to threats like Danger Ransomware. While cybercriminals continue to refine their methods, maintaining vigilance and utilizing preventative measures remain the best defense against these ever-evolving digital threats.